Excel 4 Emotet Maldoc Analysis using CyberChef
This past week I got this attachment and this time I used CyberChef [3] using the same technique published by Didier [1] last year to do a quick analysis of the file vs using oledump. I checked the SHA256 in virustotal and it showed this file had been submitted for analysis and was identified as Emotet [2].
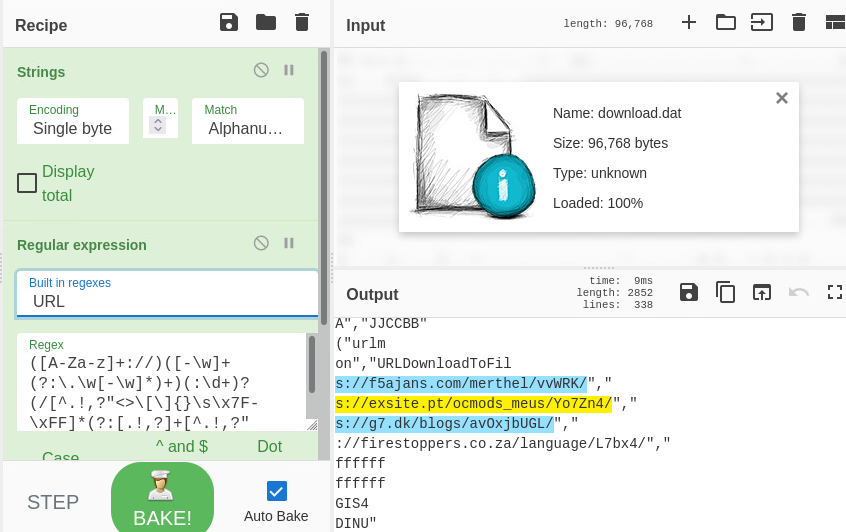
First I opened the suspicious file as input into CyberChef, next step was to applied Strings followed by Regular Expression and changed the default to URL to see if there was any URLs contained in this file.
Indicators of Compromise
SHA256: df02d16c8a18008411ad1202ff67962b656b4ea88648a1bdcfbd8030bee44381 download.dat
f5ajans[.]com/merthel/vvWRK/
exsite[.]pt/ocmods_meus/Yo7Zn4/
g7[.]dk/blogs/avOxjbUGL/
firestoppers.co[.]za/language/L7bx4/
[1] https://isc.sans.edu/forums/diary/Video+Strings+Analysis+VBA+Excel4+Maldoc/27874/
[2] https://www.virustotal.com/gui/file/df02d16c8a18008411ad1202ff67962b656b4ea88648a1bdcfbd8030bee44381
[3] https://gchq.github.io/CyberChef/
[4] https://otx.alienvault.com/indicator/domain/f5ajans.com
[5] https://otx.alienvault.com/indicator/domain/exsite.pt
[6] https://otx.alienvault.com/indicator/domain/g7.dk
[7] https://otx.alienvault.com/indicator/domain/firestoppers.co.za
-----------
Guy Bruneau IPSS Inc.
My Handler Page
Twitter: GuyBruneau
gbruneau at isc dot sans dot edu


Comments