Malicious .DAA Attachments
Reader Jason submitted a suspicious file he received via email: attachment Swift Detail.daa
After a quick Google search, I found out DAA stands for Direct Access Archive and that it is a disk image format like ISO files. Unlike ISO files, DAA files are not recognized by Windows, they won't be mounted when double clicked. Only Windows machines with installed image editing applications (like PowerISO) can open these files.
I have a license for such an application, and was able to extract the content: a single .exe file, no surprise!
This is exactly like the attacks we reported with ISO files, except that in this case, you definitively need the right application to be able to execute the embedded malware. If you don't, you can't open the DAA file to execute the embedded EXE file. I doubt that these campaigns will make a lot of victims, if any: I don't think you'll find many corporate users that are familiar with SWIFT messages and have a tool like PowerISO installed.
I did some research, and found out that the DAA format is, in a nutshell, a header followed by chunks of a compressed ISO file. There are free, open source tools to convert DAA files to ISO (e.g. extract the embedded ISO file). Like DAA2ISO.
And I started to make my own tool in Python. Not a tool to parse DAA files, but a more generic tool: a tool that scans through binary data for known compression methods and extracts the compressed data it finds. It's not ready for publication yet, but I had good results with this DAA sample:
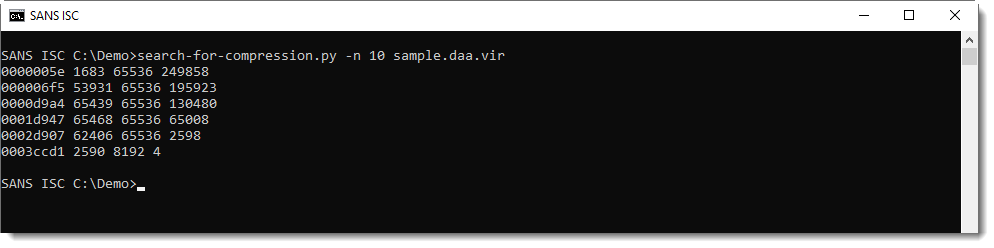
My tool found sequences of Zlib compressed chunks, that decompress to streams of 64K bytes long (65536). It looks like the DAA format consists of an ISO file chopped up in chunks of 65536 bytes, that are then compressed.
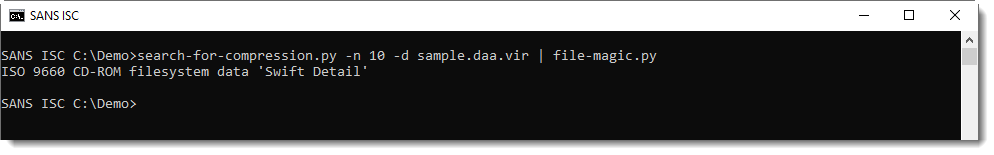
And then, I decompress all chunks to be identified by file-magic.py:
There are more formats like DAA: GBI, ISZ, ... It wouldn't surprise me if these formats starts to be used to deliver malware in a near future.
If you do find such samples, please submit them! Thanks!
Didier Stevens
Senior handler
Microsoft MVP
blog.DidierStevens.com DidierStevensLabs.com


Comments
Anonymous
Aug 14th 2019
6 years ago